Cyb(config)#router eigrp 1
Cyb(config-router)#network 10.0.0.0
Cyb(config-router)#no auto-summary
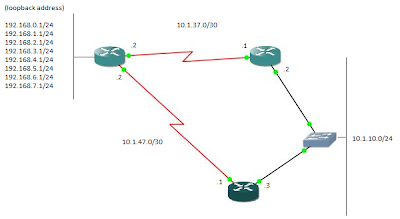
# router eigrp 1 : You can choose any number for eigrp from 1-65535, router with the same eigrp AS number will exchange routing information each others.
# network 10.0.0.0 : all the interface with this address will be advertised to all router with eigrp 1
#no auto-summary : if you are using classless IP address in your network, this command should be apply, if not, router gonna summarize all the network and only advertise it as a single network. It may cause looping problem. Classfull network not gonna effected

After eigrp is set on the 2nd router, you’ll notice there’s a message as picture above, this mean that both router are learning each other, they both advertise the network 10.x.x.x as defined in the command.
Type #show ip eigrp interface to know which interface is advertise, in this case, all the interface with address 10.x.x.x
Now we’ll configure eigrp on Aus router, but this time one by one, mean I’ll do on specific interface or subnet. Previously we did it by take the full class of 10.x.x.x IP address. We gonna start advertise subnet 10.1.37.x to eigrp 1, follow by other subnet.
Aus(config)#router eigrp 1
Aus(config-router)#network 10.1.37.0 0.0.0.255

The message show only 10.1.37.x subnet as new learned network, this example just to show how to choose any specific subnet to advertise. So now we’ll proceed to add the rest of the subnet.
Aus(config-router)#network 10.1.47.0 0.0.0.255
Aus(config-router)#network 192.168.0.0 0.0.255.255
So we added all the network that we want eigrp to learn already, now let’s check from Cyb router, type
Cyb#show ip route
from the result, we can see there are two directly connected subnet (line start with c, d is eigrp). Ok, now we know that cyb already learn about 192.168.x.x network that connected to Aus.
Simulate the backup link when the primary is down
From the topology, there are two links from Aus to reach 10.1.10.0/24, and vice versa. Let’s assume Aus – Cyb is 2xT1 line, Aus – Png is T1. How to this? Just manually set the interface bandwidth.
Aus(config)#int ser 0/0 (to Cyb)
Aus(config-if)#bandwidth 3088 (format is in kilobits)
Aus(config)#int ser 0/1 (to Png)
Aus(config-if)#bandwidth 1544 (format is in kilobits)
Type show ip route
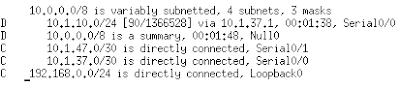
But there’s only one route to 10.1.10.x, what happen to Aus-Png? Actually eigrp only advertise the best route. Show ip route only show routing table, so to see all the learned network table(topology table), type show ip eigrp topology
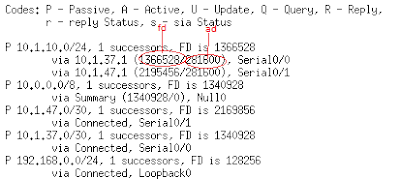
There’s a lot of information we can get from here. In red,
FD is feasible distance; cost between here(Aus) – 10.1.10.x.
AD is advertise distance; cost from neighbor to 10.1.10.x; Cyb to 10.1.10.x
codes p – passive mean the routing for this route is in idle because the link is up.
Codes A – active mean not ok; the link maybe down or not avaible, so routing protocol is actively looking for a backup or another link to this network
if you notice, AD for both router to 10.1.10.x is same, this is because both are having the same cost(bandwidth) to reach 10.1.10.x, fd is not same because the WAN link not same, Cyb use 2xT1 and Png use T1. So eigrp will choose the lowest FD as successor(primary link).
Ok, now let’s shutdown the successor, int ser 0/0 on Aus, and show ip route
Now route to 10.1.10.x is thru Png, 10.1.47.1
Default route (usually for internet)
Now let’s simulate a default route or route to the internet, let’s assume link to the internet is using loopback 0, 192.168.0.0/24 on Aus.
Aus(config)#ip route 0.0.0.0 0.0.0.0 lo 0 //this will route ‘any’ address to’ any’ address thru loopback 0
Aus(config)#router eigrp 1
Aus(config-router)#net 0.0.0.0 //advertise ‘any’ network to eigrp 1
To try this, try traceroute to 4.2.2.2, one of the internet DNS from any router(just for example) better try from Cyb or Png to make sure eigrp advertise this route to all the router within the same AS number
All the packet to the destination unknown or any or (internet) will be routed to 10.1.47.2 which is Aus. So this should be enough to prove the concept J happy routing!











